The Quantum Computing Threat to Cryptocurrency: What You Need to Know
CZ Urges Calm Amid Quantum Computing Concerns
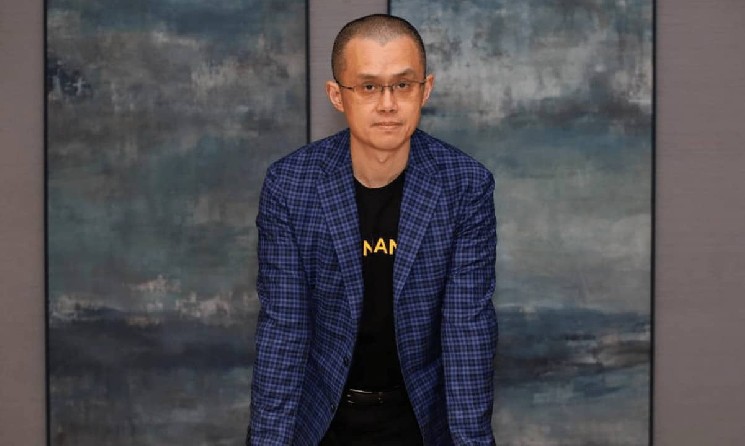
When Google dropped a bombshell research paper warning that quantum computers could crack Bitcoin and Ethereum’s cryptographic defenses with far less computing power than previously estimated, the cryptocurrency world had reason to be concerned. However, Changpeng Zhao, better known as CZ, the former CEO of Binance, took to social media platform X to offer reassurance to worried investors and crypto enthusiasts. His message was straightforward: while the threat is real, the solution is already known. According to CZ, the cryptocurrency industry simply needs to upgrade to quantum-resistant algorithms, and there’s no reason for widespread panic. While this sounds reassuring on the surface, the reality of implementing such changes across decentralized networks presents significant challenges that the industry will need to navigate carefully in the coming years.
CZ acknowledged that upgrading cryptocurrency networks isn’t as simple as pushing a software update to centralized servers. The decentralized nature of blockchain technology, which is one of its greatest strengths, also makes coordinated upgrades significantly more complicated. He predicted that the cryptocurrency community would engage in lengthy debates about which quantum-resistant algorithms to adopt, and these discussions would likely lead to network forks—situations where the blockchain splits into different versions as different groups choose different paths forward. Some projects, particularly those that have been abandoned or have minimal active development, may never upgrade at all. CZ suggested this might actually be beneficial for the industry, serving as a natural cleansing mechanism that eliminates dead or dying projects. His optimistic outlook stems from a fundamental principle of cryptography: it’s always easier to encrypt information than to decrypt it, meaning that as computing power increases for attackers, it also increases for defenders, allowing cryptocurrency to survive in a post-quantum world.
The Mystery of Satoshi’s Bitcoin Fortune
One of the most intriguing aspects of the quantum computing discussion involves the estimated one million Bitcoins believed to be held by Satoshi Nakamoto, Bitcoin’s pseudonymous creator who disappeared from public view over a decade ago. CZ raised an important question about this massive stash of cryptocurrency, which remains untouched and dormant. If these coins suddenly moved, it would confirm that Satoshi (or someone with access to those private keys) is still around and actively monitoring their fortune—an interesting revelation in itself. However, CZ suggested a more controversial scenario: if these coins remain dormant for a certain period of time, particularly as quantum computing threats become more immediate, it might be better for the Bitcoin community to lock or effectively burn those addresses. His reasoning is pragmatic—preventing these coins from falling into the hands of the first hacker who manages to crack the cryptographic protection using quantum computing technology.
Google’s research paper specifically highlighted these dormant early Bitcoin holdings as particularly vulnerable to quantum attacks. The reason lies in how these early coins were secured. They’re protected by what’s known as P2PK (Pay-to-Public-Key) scripts, the oldest type of Bitcoin transaction script and unfortunately the most vulnerable to quantum computing attacks. Unlike more modern Bitcoin addresses that use hash functions to add an extra layer of protection, P2PK scripts record the public key directly on the blockchain with no hash protection whatsoever. This creates a permanent vulnerability because a quantum attacker doesn’t need to wait for a transaction to occur—the public key is already visible on the blockchain, making these coins permanently exposed to what researchers call “at-rest attacks.” This means that even if the coins never move, a sufficiently powerful quantum computer could theoretically derive the private key from the publicly visible public key and steal the coins.
The Technical Reality: How Far Away Is the Threat?
Despite the alarming headlines, some cryptocurrency researchers are urging caution before hitting the panic button. The Bitcoin research outlet TFTC pointed out important context that often gets lost in sensational reporting: Google didn’t actually execute an attack on cryptocurrency. Instead, they published a zero-knowledge proof demonstrating that their mathematical models work and then invoked national security considerations. According to TFTC’s analysis, current quantum computers are still approximately 100,000 times weaker than what would be required to break the elliptic-curve cryptography that protects Bitcoin and most other cryptocurrencies. This suggests the industry has more time than immediate panic might suggest, though the exponential pace of quantum computing development means this window could close faster than expected.
Bitcoin developers aren’t sitting idle while quantum computers advance. They’re already working on innovative solutions designed to protect the network against future quantum threats. One promising development is called SHRIMPS—post-quantum signatures that are approximately three times smaller than the NIST (National Institute of Standards and Technology) standards. This compact size is crucial because Bitcoin’s blocks have limited space, and any security upgrade needs to work within these constraints. Additionally, developers are working on BIP-360, a Bitcoin Improvement Proposal that would introduce a quantum-resistant output type. This proposal has already been implemented on Bitcoin’s testnet, allowing developers to identify and resolve potential issues before deployment on the main network. However, not everyone shares this optimistic assessment of Bitcoin’s quantum preparedness. Crypto entrepreneur Nic Carter offered a sobering counterpoint, stating that there’s actually no formal Bitcoin Improvement Proposal, no agreed-upon post-quantum cryptographic scheme, no clear roadmap for implementation, and that most major Bitcoin developers continue to downplay or deny the severity of the quantum risk.
Satoshi’s Prophetic Warning from 2010
In an fascinating historical discovery, crypto venture capitalist Luke Martin unearthed an old comment from Satoshi Nakamoto that directly addressed the quantum computing threat to Bitcoin. Back in 2010, when a user named “llama” asked what would happen if Bitcoin’s cryptographic signatures were compromised by quantum computers and whether it would render Bitcoin worthless, Satoshi provided a thoughtful response. The Bitcoin creator acknowledged that if quantum computing capabilities emerged suddenly, it would indeed be a serious problem. However, Satoshi expressed confidence that if the threat materialized gradually, the Bitcoin network could transition to stronger cryptographic algorithms. According to Satoshi’s vision, when users ran upgraded software for the first time, it would automatically re-sign all their Bitcoin holdings using the new, quantum-resistant algorithms. This remarkably prescient comment represents the only public statement Satoshi ever made about quantum computing risks to Bitcoin, demonstrating that the creator considered this threat from the very beginning.
However, modern researchers have identified a critical constraint that Satoshi’s 2010 comment didn’t fully address. Project Eleven, an organization that has extensively documented the quantum threat to cryptocurrencies, explained that every single Bitcoin user would need to actively upgrade their holdings—this is the fundamental bottleneck that no protocol upgrade can circumvent. The reason is deeply rooted in how Bitcoin’s security model works: your coins are locked to an ECDSA (Elliptic Curve Digital Signature Algorithm) keypair, and the only way to move them to a post-quantum secured output is to sign a transaction using that ECDSA key. No soft fork or protocol-level upgrade can perform this migration on behalf of users because doing so would fundamentally break Bitcoin’s security model. This means that even if the Bitcoin network successfully upgrades to quantum-resistant algorithms, any coins held in old-style addresses that aren’t manually moved by their owners would remain vulnerable to quantum attacks. This creates a significant coordination challenge, especially for coins held by people who have lost interest in cryptocurrency, lost access to their wallets, or passed away without sharing their private keys.
The Path Forward: Challenges and Opportunities
The quantum computing threat to cryptocurrency represents both a significant challenge and an opportunity for the industry to demonstrate its resilience and adaptability. While the technical solutions exist—quantum-resistant cryptographic algorithms have been developed and tested—implementing them across decentralized networks with millions of users presents unprecedented coordination challenges. The cryptocurrency community will need to engage in difficult conversations about which algorithms to adopt, how to handle coins that can’t be upgraded because their owners are unreachable, and what to do about particularly vulnerable legacy addresses like those holding Satoshi’s estimated million Bitcoins. These debates will likely be contentious, with different factions advocating for different approaches, potentially leading to network forks that could temporarily divide communities and create confusion in the market.
Despite these challenges, the cryptocurrency industry has successfully navigated major upgrades before. Ethereum’s transition from proof-of-work to proof-of-stake demonstrated that even fundamental changes to how a blockchain operates can be accomplished with careful planning, extensive testing, and community coordination. The quantum threat may actually serve as a catalyst for removing defunct projects from the ecosystem and strengthening the networks that remain through forced upgrades. As CZ noted, the fundamental mathematics of cryptography favor defenders—encryption will always be easier than decryption, and the same technological advances that empower quantum computers to break current cryptography also enable the development of stronger quantum-resistant alternatives. The cryptocurrency industry has several years to prepare, but the time to begin serious implementation of quantum-resistant upgrades is now, before the threat becomes immediate. Those projects that successfully navigate this transition will emerge stronger and more secure, while those that fail to adapt will be left behind, ultimately creating a more resilient cryptocurrency ecosystem for the post-quantum era.